Build apps users love with AI-driven insights
Power your mobile and web apps at scale with the most comprehensive solution for software quality. Test, release, and innovate confidently with AI-driven insights grounded in real data.
8+bn
TESTS EXECUTED
300k
ACTIVE USERS
9000+
REAL DEVICES
2500+
EMUSIMS AND BROWSER/OSES
Selenium founders - loved by devs, trusted by enterprises
ENTERPRISE-READY. AI-DRIVEN. ONE UNIFIED VIEW.
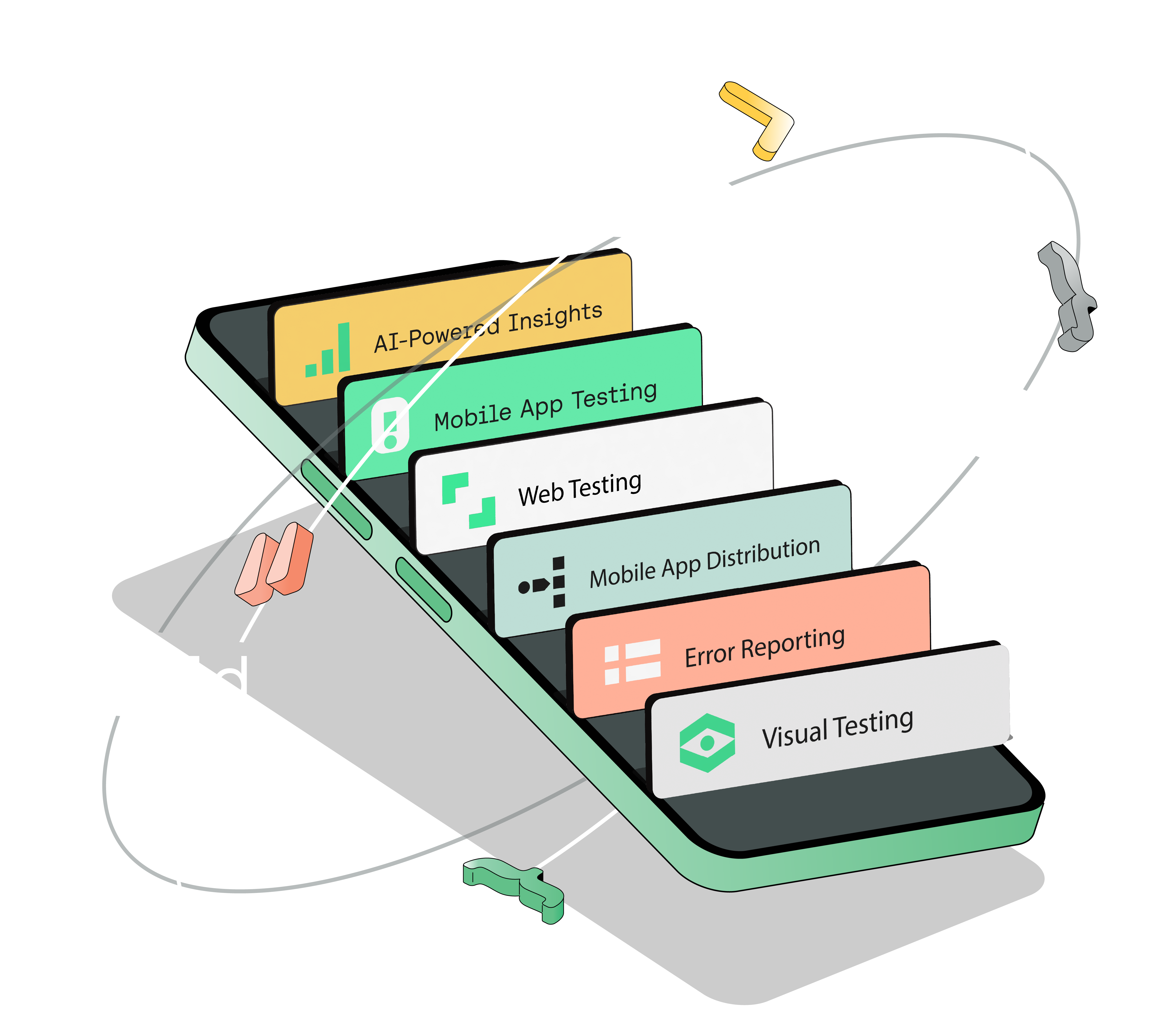
One Platform for Continuous Quality
Ensure quality at every stage of development with AI-powered insights. Access the widest selection of real devices, virtual emulators and simulators, and browsers/OS support, plus streamlined app distribution and error reporting—all in one powerful platform.
CASE STUDIES
The secret sauce behind every great app
Discover how leading brands deliver high-quality digital experiences with Sauce Labs.